For a detail serach, try google search!!
Hacking Windows Media Player !!
You can change the title bar for the Windows Media Player
1. Start Regedit
2. Go to HKEY_USERS \ .DEFAULT \ Software \ Policies \ Microsoft \ WindowsMediaPlayer
3. Create a string value of TitleBar
4. Give it a value of whatever you want to appear in the title bar
Hacking into XP !!
Here is a technique to change XP password of your friend's login pc without knowing any hint or old passwords:
just open CMD PROMPT and type as shown below
C:/ net user username newpassword <----|
for example...
If your friend's username is Gaurav, and you want to change itz password to Bhatia
Type as shown below:
C:/net user Gaurav Bhatia <====
tats all u have successfully changed ur friendz password to "Bhatia"
If you are the admin of pc then go to CMD prompt and type
"""""control userpasswords2""""""
here you can change the password
Windows Hack: Disable Windows Genuine Advantage Notification
Following three simple steps now you can get rid of the pesky and sometimes buggy Windows Genuine Advantage (WGA) notifications:
1. Reboot Windows in safe mode (hold the f8 key while booting and you will get the option to boot in safe mode) and then:
2. Open Registry Editor (regedit.exe) and search for wgalogon folder and delete it. You should backup up the registry beforehand, in case somethiong goes wrong.
3. In your windows directory search for files wga* and delete them.
You are done!
Now reboot back normally and continue your work. Windows Genuine Advantage will not bother you anymore.
Warning: Use at your own risk. Backup everything before you do.
How To Change Your Motherboard Battery
First the safety rules!The inside of a computer is a bad place full of electricity and sharp edges.
On the electricity side always when working on you computer make sure that it’s still plugged in to the power socket and the power is turned off, this is to ensure that any static
From you is discharged through the earth. The inside of most computer cases are unfinished metal and has very sharp edges so be careful.
The first signs of a battery failing are:
- Your clock starts running slowly
- When you boot (start) your computer it has a problem finding your hardware (no hard drive, no cd rom)
To change the battery you need the following tools:
- a X-point screwdriver
- an anti-static strap(optional)
- a new battery (seems logical)

Then unplug all the cables from the back of the computer as you remove them make a note where they came from. (So when you finished you can put them back).
Move the computer somewhere where you can work on it with ease
Remove the cover by locating the screws around the outer edge (back) of the computer
Some computer cases only require you to remove 2 screws on one side then a panel can be removed allowing you access to the computers insides, others you must remove 6 screws and remove the whole case by sliding it to the rear and lifting it off.

Now make sure that you read the safety instructions about static.
Look inside you will see a round silver thing that looks about the size of a 10p piece (quarter). This is the battery itself, carefully lift the retaining clip and slide the battery out. That’s it removed now go to your local computer retailer, electrical retailer (Tandy/Radio shack) taking the old battery with you and get a new battery.
Back to your computer insert the new battery by lifting the clip and sliding the battery in.
Reinstall your case and plug all the cables back (you did remember to label them didn’t you)
Turn on your PC. You will now need to go into you bios….
Right the bios is the god of your computer. To access it, when your computer first starts you will see a black screen with white text.
If you look carefully you will see a line that says something like "press del for setup" or some other key (F2 or ESC or tab) this will take you to god's house where you can make lots of changes to the way your machine works.
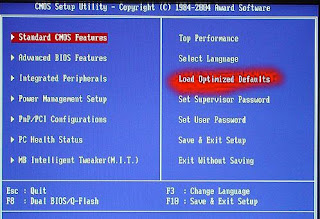
It is also the place where you can make your nice computer in to a rather expensive door stop so be careful and don’t go playing with anything.
You will now be presented with a blue screen with a lot of options on it, the one we want is Load Optimised / Default settings.
Press the F10 key for save setting and type Y, the computer should now reboot.
If every thing went well then your computer will now be up and running.
Extreme way (NOT RECOMMENDED):
- Keep computer running.
- Lay it on it's side and remove side cover to expose Motherboard.
- Take any thin object, "small screwdriver, knife point, wood shiskabob skewer.
- Pull back the battery retaining clip.
- Toss the old battery in the junk receptacle, unless you belong to Greenpeace and want to save the earth.
- Install the new battery. No need to reset bios becasue the compter supplies voltage to the CMOS while it is running.
- Reset or resync clock with internet. Done!
Cracking Password Protected Zip Files
What is FZC?
FZC is a program that cracks zip files (zip is a method of compressing multiple files into one smaller file) that are password-protected (which means you’re gonna need a password to open the zip file and extract files out of it). You can get it anywhere - just use a search engine such as google.com.
FZC uses multiple methods of cracking - bruteforce (guessing passwords systematically until the program gets it) or wordlist attacks (otherwise known as dictionary attacks. Instead of just guessing passwords systematically, the program takes passwords out of a “wordlist”, which is a text file that contains possible passwords. You can get lots of wordlists at www.theargon.com.).
FZC can be used in order to achieve two different goals: you can either use it to recover a lost zip password which you used to remember but somehow forgot, or to crack zip passwords which you’re not supposed to have. So like every tool, this one can be used for good and for evil.
The first thing I want to say is that reading this tutorial… is the easy way to learn how to use this program, but after reading this part of how to use the FZC you should go and check the texts that come with that program and read them all. You are also going to see the phrase “check name.txt” often in this text. These files should be in FZC’s directory. They contain more information about FZC.
FZC is a good password recovery tool, because it’s very fast and also supportcomputer turned on until you get the password, like it used to be some years ago with older cracking programs. You would probably always get the password unless the password is longer than 32 chars (a char is a character, which can be anything - a number, a lowercase or undercase letter or a symbol such as ! or &) because 32 chars is the maximum value that FZC will accept, but it doesn’t really matter, because in order to bruteforce a password with 32 chars you’ll need to be at least immortal..heehhe.. to see the time that FZC takes with bruteforce just open the Bforce.txt file, which contains such information. resuming so you don’t have to keep the
FZC supports brute-force attacks, as well as wordlist attacks. While brute-force attacks don’t require you to have anything, wordlist attacks require you to have wordlists, which you can get from www.theargon.com. There are wordlists in various languages, various topics or just miscellaneous wordlists. The bigger the wordlist is, the more chances you have to crack the password.
Now that you have a good wordlist, just get FZC working on the locked zip file, grab a drink, lie down and wait… and wait… and wait…and have good thoughts like “In wordlist mode I’m gonna get the password in minutes” or something like this… you start doing all this and remember “Hey this guy started with all this bullshit and didn’t say how I can start a wordlist attack!…” So please wait just a little more, read this tutorial ’till the end and you can do all this “bullshit”.
We need to keep in mind that are some people might choose some really weird passwords (for example: ‘e8t7@$^%*gfh), which are harder to crack and are certainly impossible to crack (unless you have some weird wordlist). If you have a bad luck and you got such a file, having a 200MB list won’t help you anymore. Instead, you’ll have to use a different type of attack. If you are a person that gives up at the first sign of failure, stop being like that or you won’t get anywhere. What you need to do in such a situation is to put aside your sweet xxx MB’s list and start using the Brute Force attack.
If you have some sort of a really fast and new computer
Now that we’ve gone through all the theoretical stuff, let’s get to the actual commands.
Bruteforce
The command line you’ll need to use for using brute force is:
fzc -mb -nzFile.zip -lChr Lenght -cType of chars
Now if you read the bforce.txt that comes with fzc you’ll find the description of how works Chr Lenght and the Type of chars, but hey, I’m gonna explain this too. Why not, right?… (but remember look at the bforce.txt too)
For Chr Lenght you can use 4 kind of switches…
-> You can use range -> 4-6 :it would brute force from 4 Chr passwors to 6 chr passwords
-> You can use just one lenght -> 5 :it would just brute force using passwords with 5 chars
-> You can use also the all number -> 0 :it would start brute forcing from passwords with lenght 0 to lenght 32, even if you are crazy i don’t think that you would do this…. if you are thinking in doing this get a live…
-> You can use the + sign with a number -> 3+ :in this case it would brute force from passwords with lenght 3 to passwords with 32 chars of lenght, almost like the last option…
For the Type of chars we have 5 switches they are:
-> a for using lowercase letters
-> A for using uppercase letters
-> ! for using simbols (check the Bforce.txt if you want to see what simbols)
-> s for using space
-> 1 for using numbers
Example:
If you want to find a password with lowercase and numbers by brute force you would just do something like:
fzc -mb -nzTest.zip -l4-7 -ca1
This would try all combinations from passwords with 4 chars of lenght till 7 chars, but just using numbers and lowercase.
*****
hint
*****
You should never start the first brute force attack to a file using all the chars switches, first just try lowercase, then uppercase, then uppercase with number then lowercase with numbers, just do like this because you can get lucky and find the password much faster, if this doesn’t work just prepare your brain and start with a brute force that would take a lot of time. With a combination like lowercase, uppercase, special chars and numbers.
Wordlist
Like I said in the bottom and like you should be thinking now, the wordlist is the most powerfull mode in this program. Using this mode, you can choose between 3 modes, where each one do some changes to the text that is in the wordlist, I’m not going to say what each mode does to the words, for knowing that just check the file wlist.txt, the only thing I’m going to tell you is that the best mode to get passwords is mode 3, but it takes longer time too.
To start a wordlist attak you’ll do something like.
fzc -mwMode number -nzFile.zip -nwWordlist
Where:
Mode number is 1, 2 or 3 just check wlist.txt to see the changes in each mode.
File.zip is the filename and Wordlist is the name of the wordlist that you want to use. Remember that if the file or the wordlist isn’t in the same directory of FZC you’ll need to give the all path.
You can add other switches to that line like -fLine where you define in which line will FZC start reading, and the -lChar Length where it will just be read the words in that char length, the switche works like in bruteforce mode.
So if you something like
fzc -mw1 -nztest.zip -nwMywordlist.txt -f50 -l9+
FZC would just start reading at line 50 and would just read with length >= to 9.
Example:
If you want to crack a file called myfile.zip using the “theargonlistserver1.txt” wordlist, selecting mode 3, and you wanted FZC to start reading at line 50 you would do:
fzc -mw3 -nzmyfile.zip -nwtheargonlistserver1.txt -f50
Resuming
Other good feature in FZC is that FZC supports resuming. If you need to shutdown your computer and FZC is running you just need to press the ESC key, and fzc will stop. Now if you are using a brute force attack the current status will be saved in a file called resume.fzc but if you are using a wordlist it will say to you in what line it ended (you can find the line in the file fzc.log too).
To resume the bruteforce attack you just need to do:
fzc -mr
And the bruteforce attack will start from the place where it stopped when you pressed the ESC key.
But if you want to resume a wordlist attack you’ll need to start a new wordlist attack, saying where it’s gonna start. So if you ended the attack to the file.zip in line 100 using wordlist.txt in mode 3 to resume you’ll type
fzc -mw3 -nzfile.zip -nwwordlist.txt -f100
Doing this FZC would start in line 100, since the others 99 lines where already checked in an earlier FZC session.
Well, it looks like I covered most of what you need to know. I certainly hope it helped you… don’t forget to read the files that come with the program
20 Great Google Secrets
Google is clearly the best general-purpose search engine on the Web
But most people don’t use it to its best advantage. Do you just plug in a keyword or two and hope for the best? That may be the quickest way to search, but with more than 3 billion pages in Google’s index, it’s still a struggle to pare results to a manageable number.
But Google is an remarkably powerful tool that can ease and enhance your Internet exploration. Google’s search options go beyond simple keywords, the Web, and even its own programmers. Let’s look at some of Google’s lesser-known options.
Syntax Search Tricks
Using a special syntax is a way to tell Google that you want to restrict your searches to certain elements or characteristics of Web pages. Google has a fairly complete list of its syntax elements at:
www.google.com/help/operators.html
Here are some advanced operators that can help narrow down your search results.
Intitle: at the beginning of a query word or phrase (intitle:”Three Blind Mice”) restricts your search results to just the titles of Web pages.
Intext: does the opposite of intitle:, searching only the body text, ignoring titles, links, and so forth. Intext: is perfect when what you’re searching for might commonly appear in URLs. If you’re looking for the term HTML, for example, and you don’t want to get results such as
www.mysite.com/index.html
You can also enter intext:html.
Link: lets you see which pages are linking to your Web page or to another page you’re interested in. For example, try typing in
link:http://www.hungry-hackers.com
Try using site: (which restricts results to top-level domains) with intitle: to find certain types of pages. For example, get scholarly pages about Mark Twain by searching for intitle:”Mark Twain”site:edu. Experiment with mixing various elements; you’ll develop several strategies for finding the stuff you want more effectively. The site: command is very helpful as an alternative to the mediocre search engines built into many sites.
Swiss Army Google
Google has a number of services that can help you accomplish tasks you may never have thought to use Google for. For example, the new calculator feature
(www.google.com/help/features.html#calculator)
Lets you do both math and a variety of conversions from the search box. For extra fun, try the query “Answer to life the universe and everything.”
Let Google help you figure out whether you’ve got the right spelling—and the right word—for your search. Enter a misspelled word or phrase into the query box (try “thre blund mise”) and Google may suggest a proper spelling. This doesn’t always succeed; it works best when the word you’re searching for can be found in a dictionary. Once you search for a properly spelled word, look at the results page, which repeats your query. (If you’re searching for “three blind mice,” underneath the search window will appear a statement such as Searched the web for “three blind mice.”) You’ll discover that you can click on each word in your search phrase and get a definition from a dictionary.
Suppose you want to contact someone and don’t have his phone number handy. Google can help you with that, too. Just enter a name, city, and state. (The city is optional, but you must enter a state.) If a phone number matches the listing, you’ll see it at the top of the search results along with a map link to the address. If you’d rather restrict your results, use rphonebook: for residential listings or bphonebook: for business listings. If you’d rather use a search form for business phone listings, try Yellow Search
(www.buzztoolbox.com/google/yellowsearch.shtml).
Extended Googling
Google offers several services that give you a head start in focusing your search. Google Groups
(http://groups.google.com)
indexes literally millions of messages from decades of discussion on Usenet. Google even helps you with your shopping via two tools: Froogle
CODE
(http://froogle.google.com),
which indexes products from online stores, and Google Catalogs
CODE
(http://catalogs.google.com),
which features products from more 6,000 paper catalogs in a searchable index. And this only scratches the surface. You can get a complete list of Google’s tools and services at
www.google.com/options/index.html
You’re probably used to using Google in your browser. But have you ever thought of using Google outside your browser?
Google Alert
(www.googlealert.com)
monitors your search terms and e-mails you information about new additions to Google’s Web index. (Google Alert is not affiliated with Google; it uses Google’s Web services API to perform its searches.) If you’re more interested in news stories than general Web content, check out the beta version of Google News Alerts
(www.google.com/newsalerts).
This service (which is affiliated with Google) will monitor up to 50 news queries per e-mail address and send you information about news stories that match your query. (Hint: Use the intitle: and source: syntax elements with Google News to limit the number of alerts you get.)
Google on the telephone? Yup. This service is brought to you by the folks at Google Labs
(http://labs.google.com),
a place for experimental Google ideas and features (which may come and go, so what’s there at this writing might not be there when you decide to check it out). With Google Voice Search
(http://labs1.google.com/gvs.html),
you dial the Voice Search phone number, speak your keywords, and then click on the indicated link. Every time you say a new search term, the results page will refresh with your new query (you must have JavaScript enabled for this to work). Remember, this service is still in an experimental phase, so don’t expect 100 percent success.
In 2002, Google released the Google API (application programming interface), a way for programmers to access Google’s search engine results without violating the Google Terms of Service. A lot of people have created useful (and occasionally not-so-useful but interesting) applications not available from Google itself, such as Google Alert. For many applications, you’ll need an API key, which is available free from
CODE
www.google.com/apis
Thanks to its many different search properties, Google goes far beyond a regular search engine. Give the tricks in this article a try. You’ll be amazed at how many different ways Google can improve your Internet searching.
Online Extra: More Google Tips
Here are a few more clever ways to tweak your Google searches.
Search Within a Timeframe
Daterange: (start date–end date). You can restrict your searches to pages that were indexed within a certain time period. Daterange: searches by when Google indexed a page, not when the page itself was created. This operator can help you ensure that results will have fresh content (by using recent dates), or you can use it to avoid a topic’s current-news blizzard and concentrate only on older results. Daterange: is actually more useful if you go elsewhere to take advantage of it, because daterange: requires Julian dates, not standard Gregorian dates. You can find converters on the Web (such as
CODE
http://aa.usno.navy.mil/data/docs/JulianDate.html
excl.gif No Active Links, Read the Rules - Edit by Ninja excl.gif), but an easier way is to do a Google daterange: search by filling in a form at
www.researchbuzz.com/toolbox/goofresh.shtml or www.faganfinder.com/engines/google.shtml
If one special syntax element is good, two must be better, right? Sometimes. Though some operators can’t be mixed (you can’t use the link: operator with anything else) many can be, quickly narrowing your results to a less overwhelming number.
More Google API Applications
Staggernation.com offers three tools based on the Google API. The Google API Web Search by Host (GAWSH) lists the Web hosts of the results for a given query
(www.staggernation.com/gawsh/).
When you click on the triangle next to each host, you get a list of results for that host. The Google API Relation Browsing Outliner (GARBO) is a little more complicated: You enter a URL and choose whether you want pages that related to the URL or linked to the URL
(www.staggernation.com/garbo/).
Click on the triangle next to an URL to get a list of pages linked or related to that particular URL. CapeMail is an e-mail search application that allows you to send an e-mail to google@capeclear.com with the text of your query in the subject line and get the first ten results for that query back. Maybe it’s not something you’d do every day, but if your cell phone does e-mail and doesn’t do Web browsing, this is a very handy address to know.
Vodafone Hack for Free GPRS
Followng are the Settings you require to configure on your Mobile:
Account Name: Vodafone_gprs
Homepage: http://live.vodafone.in
User Name: (no need)
Pass: (no need)
Access Point Settings:
Proxy: Enabled
Proxy Address: 10.10.1.100
Proxy Port: 9401
Data Bearer: Packet Data
Bearer Settings:
Packet Data Access Point: portalnmms
Network type: IPV4
Authentication: normal
User Name: (no need)
Password: (no need)
*IF that happen this settings is not working then change the proxy port number to:-
Proxy Port: 9401
Free RapidShare and MegaUpload Premium Accounts
Everyone wants a free Rapidshare Premium Account! Not everyone can afford the ten bucks it costs per month. If you’re one of them, read on.
Today I am going to tell a Full Proof way of Getting a Free RapidShare or MegaUpload Premium Accounts.
Using this Method you can actually get you Real Money using which you can buy anything:
Follow these steps:
1. Create a Paypal Premium Account( Don’t Worry its free) . When asked for credit card details simply say cancel. You do not need to fill it.
2. Then Go to the following link:
3. Join this site. It is also free. You get paid for completing surveys over there 6$ to 4$ dollars per survey and 1.25$ per referral that’s a lot you will get a premium account of 1 year in NO TIME.
4. Another thing you can also use Paypal money to buy stuff on Ebay and other shopping sites.
5. Thats is it. So Simple and I swear it works.
Security Hack : Three Most used Backdoor Programs
There is a general misconception about security today. Most people would love to believe that their firewalls are completely capable to protect them from anything indecent. The sad part, they could not be more wrong. Hungry Hacker aim to prove it with three separate programs that can compromise the security
Using these programs any noob can remotely access your computer without any Authentication and do whatever he wants. I will tell you some of the features rest of them you need to try it and find out. These Programs :
- Work as a key logger.
- Send any Information from Victim’s PC to the Hacker’s PC.
- Run any program on the Victims PC.
- Display any Violating Image on victim’s Screen.
- Open the CD Drive of the Victim’s PC.
- Open any Web page on the Victims Screen.
- Disable any Specific Key or whole Keyboard.
- Shutdown Victim’s PC.
- Start a Song on the Victim’s PC.etc.etc…………..
Back Orifice / Back Orifice 2000
Back Orifice is one of the most common backdoor programs, and one of the most deadly. The name may seem like a joke, but sure, the threat is real. Back Orifice was established in Cult of the Dead Cow group. Back Orifice is an Open Source Program. The main Threat of this software is that by making some changes in the code anybody can make it undetectable to the Anti virus Program running on the Victim’s computer. Apart from the strange title, the program usually gets port 31337, the reference to “Lit” phenomenon is popular among hackers.
Back Orifice uses a client-server model, while the server and client is the victim attacker. What makes Back Orifice so dangerous that it can install and operate silently. There is not required interaction with the user in, meaning you could its on your computer right now, and do not know.
Companies such as Symantec have taken steps to protect computers against programs that they consider dangerous. But even more attacks using Back Orifice 2000. This is due partly to the fact that it is still evolving, as open source. As stated in the documentation the goal is ultimately the presence of the Back Orifice 2000 unknown even to those who installed it.
Back Orifice 2000, developed for Windows
Where can I download Back orifice 2000?
Back Orifice 2000 can be downloaded at the following address: http://sourceforge.net/projects/bo2k/
I infected! How do I remove it?
Removing Back Orifice 2000 may require that you change the registry settings. To remove it at 7 simple steps, refer to the diagram below.
How do I delete Back orifice 2000
- Click Start> Run, and type “Regedit”(without the quotes)
- Follow the path below: HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServices “
- Now looking in the right box: “The umgr32 = ‘c: \ windows \ system \ umgr32.exe”
- Right-click on this entry and click Remove. Now restart your computer.
- After restarting only open Windows Explorer. Make sure you can see all registered extensions. To do so, select “View Options and configure the appropriate settings.
- Go to the WINDOWS \ SYSTEM directory, and find “umgr32.exe” file. Once you find it, delete it.
- Exit Windows Explorer and reboot again.
NetBus / Netbus 2.0 Pro
NetBus was established around the same time that the Back Orifice was in the late 1990’s. NetBus was originally designed as a program prank friends and family, of course anything too malicious. However, the program was released in 1998, and is widely used as a backdoor to manage computer.
Like the Back Orifice, NetBus allows attackers to do virtually everything in the computer victim. It also works well under Windows 9x systems, as well as Windows XP. Unlike Back Orifice, the latest version of NetBus regarded shareware is not free. NetBus is also implementing less stealthy operations, as a direct result of criticism and complaints of abusive use.
Where can I buy and download NetBus?
NetBus can be purchased and downloaded at the following address: http://www.netbus.org/
Ok, I am infected. Now what?
Fortunately, the latest version of NetBus is a valid program. It can be removed just like any other program. Previous issuance NetBus is a bit more tricky, however. If you are not lucky enough attacked with the latest version, the withdrawal process and in the Back Orifice.
How do I remove NetBus?
- Click Start> Run, and type “Regedit ‘(without the quotes)
- Follow the path below: HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunServices “
- Now, in the right box, looking as follows: “[Name_of_Server].”Exe Of course, you have to find the actual name of this file EXE-. Usually This” Patch.exe ‘or’ SysEdit.exe “, but may vary.
- Reboot and remove all traces of the actual program, which can be left. Additionally, you can set yourself NetBus, and then use its own function disposal.
SubSeven / Sub7
SubSeven or Sub7, has been established for the same purpose was to NetBus pranks. Sub7 actually has more support for pranks, and has more advanced users. Sub7 also widely used by the script kiddies, although that many firewalls and anti-virus software before initialization.
Since Sub7 not supported for several years, the threat is usually very low. Most security programs will not have any problem in ending Sub7 before it has a chance to be started. This shows that the importance to the modernization and security programs is critical, because the money was still there.
Nevertheless, it is widely used by those who have physical access to your firewall, or security programs. If access rights
Where can I buy and download Sub7?
Sub7 not supported more, and hence is not available for download on any legitimate websites. If you were to make a Google search, you would find links to download Sub7. However, this is not the official site, and should be considered dubious and dangerous.
Sounds harmless, How do I remove it?
- End of the following processes through the curator: “editserver.exe, subseven.exe”
- Delete the following files: “editserver.exe, subseven.exe, tutorial.txt.”
Why these programs is absolutely legitimate?
All the basis behind these programs is that they are designed to help people, not harm. While some like NetBus really were originally created for pranks, they switched routes to avoid legal problems.
These programs claim to be the legitimate remote desktop program, although they certainly easily used for malicious use. These programs really should be used to aid or customer support departments. Why all adolescents is to copy these programs goes beyond us, but leave the content of their networks, while computer is a good idea.
The advent of new technology has made these programs in some respects less effective. However, programs such as Back Orifice 2000, yet still evolving, so do not be surprised to learn that he works in the background, waiting for instructions. Since the best defense is a good offense, be sure to save a sharp eye on what is installed on the network computers. After all, an ounce of prevention is worth a pound of cure.
Make FREE Calls to Landline and Mobile phones
Make FREE calls quickly
Simply type gizmocall.com/ browser bar.
(put the number you want to dial in place of 18005551212) into your
Make FREE calls to landline and mobile phones in over 60 countries by participating in the All Calls Free plan.
Users
Get Started Now!
- Tell a friend to download Gizmo5 and have them add their phone number to their profile.
- Add each other to your contact lists and you can call that person for FREE using Gizmo5.
- Be sure to make at least 1 Gizmo5 to Gizmo5 call per week or your free minutes will expire.
Get a Call from God
Came accross a truely amazing trick . And it worked for me . Here is the procedure.
Just give a missed call on +41445804650 and u’ll get a call back from your own number…
U wont be charged anything for giving missed call.
I did try to google it and came accross this article in yahoo answers.
Seems to be a new Telecom technology. Whatever it is surely it is a strange!!! [ A bit like chetan bhagat`s "one night @ a call center"]
19 Secrets about Windows XP
You’ve read the reviews and digested the key feature enhancements and operational changes. Now it’s time to delve a bit deeper and uncover some of Windows XP
1. It boasts how long it can stay up. Whereas previous versions of Windows were coy about how long they went between boots, XP is positively proud of its stamina. Go to the Command Prompt in the Accessories menu from the All Programs start button option, and then type ’systeminfo’. The computer will produce a lot of useful info, including the uptime. If you want to keep these, type ’systeminfo > info.txt’. This creates a file called info.txt you can look at later with Notepad. (Professional Edition only).
2. You can delete files immediately, without having them move to the Recycle Bin first. Go to the Start menu, select Run… and type ‘gpedit.msc’; then select Userinterface and system options, but take care — some may stop your computer behaving as you wish. (Professional Edition only). Configuration, Administrative Templates, Windows Components, Windows Explorer and find the Do not move deleted files to the Recycle Bin setting. Set it. Poking around in gpedit will reveal a great many
3. You can lock your XP workstation with two clicks of the mouse. Create a new shortcut on your desktop using a right mouse click, and enter ‘rundll32.exe user32.dll,LockWorkStation’ in the location field. Give the shortcut a name you like. That’s it — just double click on it and your computer will be locked. And if that’s not easy enough, Windows key + L will do the same.
4. XP hides some system software you might want to remove, such as Windows Messenger
5. For those skilled in the art of DOS batch files, XP has a number of interesting new commands. These include ‘eventcreate’ and ‘eventtriggers’ for creating and watching system events, ‘typeperf’ for monitoring performance of various subsystems, and ’schtasks’ for handling scheduled tasks. As usual, typing the command name followed by /? will give a list of options — they’re all far too baroque to go into here.
6. XP has IP version 6 support — the next generation of IP. Unfortunately this is more than your ISP has, so you can only experiment with this on your LAN. Type ‘ipv6 install’ into Run… (it’s OK, it won’t ruin your existing network setup) and then ‘ipv6 /?’ at the command line to find out more. If you don’t know what IPv6 is, don’t worry and don’t bother.
7. You can at last get rid of tasks on the computer from the command line by using ‘taskkill /pid’ and the task number, or just ‘tskill’ and the process number. Find that out by typing ‘tasklist’, which will also tell you a lot about what’s going on in your system.
8. XP will treat Zip files like folders, which is nice if you’ve got a fast machine. On slower machines, you can make XP leave zip files well alone by typing ‘regsvr32 /u zipfldr.dll’ at the command line. If you change your mind later, you can put things back as they were by typing ‘regsvr32 zipfldr.dll’.
9. XP has ClearType — Microsoft’s anti-aliasing font display technology — but doesn’t have it enabled by default. It’s well worth trying, especially if you were there for DOS and all those years of staring at a screen have given you the eyes of an astigmatic bat. To enable ClearType, right click on the desktop, select Properties, Appearance, Effects, select ClearType from the second drop-down menu and enable the selection. Expect best results on laptop displays. If you want to use ClearType on the Welcome login screen as well, set the registry entry HKEY_USERS/.DEFAULT/Control Panel/Desktop/FontSmoothingType to 2.
10. You can use Remote Assistance to help a friend who’s using network address translation (NAT) on a home network, but not automatically. Get your pal to email you a Remote Assistance invitation and edit the file. Under the RCTICKET attribute will be a NAT IP address, like 192.168.1.10. Replace this with your chum’s real IP address — they can find this out by going to http://www.whatismyip.com — and get them to make sure that they’ve got port 3389 open on their firewall and forwarded to the errant computer.
11. You can run a program as a different user without logging out and back in again. Right click the icon, select Run As… and enter the user name and password you want to use. This only applies for that run. The trick is particularly useful if you need to have administrative permissions to install a program, which many require. Note that you can have some fun by running programs multiple times on the same system as different users, but this can have unforeseen effects.
12. Windows XP can be very insistent about you checking for auto updates, registering a Passport, using Windows Messenger and so on. After a while, the nagging goes away, but if you feel you might slip the bonds of sanity before that point, run Regedit, go to HKEY_CURRENT_USER/Software/Microsoft/Windows/Current Version/Explorer/Advanced and create a DWORD value called EnableBalloonTips with a value of 0.
13. You can start up without needing to enter a user name or password. Select Run… from the start menu and type ‘control userpasswords2′, which will open the user accounts application
14. Internet Explorer 6 will automatically delete temporary files, but only if you tell it to. Start the browser, select Tools / Internet Options… and Advanced, go down to the Security area and check the box to Empty Temporary Internet Files folder when browser is closed.
15. XP comes with a free Network Activity Light, just in case you can’t see the LEDs twinkle on your network card. Right click on My Network Places on the desktop, then select Properties. Right click on the description for your LAN or dial-up connection, select Properties, then check the Show icon in notification area when connected box. You’ll now see a tiny network icon on the right of your task bar that glimmers nicely during network traffic.
16. The Start Menu can be leisurely when it decides to appear, but you can speed things along by changing the registry entry HKEY_CURRENT_USER/Control Panel/Desktop/MenuShowDelay from the default 400 to something a little snappier. Like 0.
17. You can rename loads of files at once in Windows Explorer. Highlight a set of files in a window, then right click on one and rename it. All the other files will be renamed to that name, with individual numbers in brackets to distinguish them. Also, in a folder you can arrange icons in alphabetised groups by View, Arrange Icon By… Show In Groups.
18. Windows Media Player will display the cover art for albums as it plays the tracks — if it found the picture on the Internet when you copied the tracks from the CD. If it didn’t, or if you have lots of pre-WMP music files, you can put your own copy of the cover art in the same directory as the tracks. Just call it folder.jpg and Windows Media Player will pick it up and display it.
19. Windows key + Break brings up the System Properties dialogue box; Windows key + D brings up the desktop; Windows key + Tab moves through the taskbar buttons.
Get free Rapidshare and mega upload accounts!!
Everyone wants a free Rapidshare Premium Account! Not everyone can afford the ten bucks it costs per month. If you’re one of them, read on.
Today I am going to tell a Full Proof way of Getting a Free RapidShare or MegaUpload Premium Accounts.
Using this Method you can actually get you Real Money using which you can buy anything:
Follow these steps:
1. Create a Paypal Premium Account( Don’t Worry its free) . When asked for credit card details simply say cancel. You do not need to fill it.
2. Then Go to the following link:
3. Join this site. It is also free. You get paid for completing surveys over there 6$ to 4$ dollars per survey and 1.25$ per referral that’s a lot you will get a premium account of 1 year in NO TIME.
4. Another thing you can also use Paypal money to buy stuff on Ebay and other shopping sites.


